Following months of testing, Plex has started to roll out its redesigned mobile app to Android and iOS devices, and it will arrive to everyone within the next week. The new app comes with an updated navigation system that should make it easier to access different parts of the app and find content to watch, along with a dedicated tab for centralized media libraries.
It also has a button in the top-right corner of the screen for your Watchlist and more artwork across detail pages for shows and movies, as well as cast and crew profiles. In a post on the Plex forum, the company outlines a ton of improvements it has made to the app since the preview, including faster load times and scrolling, the addition of a sleep timer, and picture-in-picture support.
I’ve also rolled out my big upgrade: Jellyfin
Why does plex need all of this shit? I literally only wanted to use it to stream my local stuff. Now that’s just a tiny part of the app.
I say now, but I don’t think I’ve used it at all in the past couple of years.
Enshittening
And Jellyfin is better and free. I don’t trust Plex with my content and I don’t want their added streaming bloatware.
In some ways it is… In others it’s definitely not.
My biggest problem is that I can’t expose it on a domain for my family to get to. They don’t know how to VPN and to educate them would be exhausting.
Because a reverse proxy doesn’t resolve any of these major issues.
https://github.com/jellyfin/jellyfin/issues/5415
Your content can be probed, identified, and streamed all without auth. Your users can be enumerated in certain cases.
Edit: If you host legit content, like family videos… All of that can be leaked. If you don’t host legit content… and the public site gets probed and they identify the illegal content… expect to be named in a very large lawsuit… either situation is bad.
Edit2: and hosting it behind a proxy that does it’s own auth would break ALL app-based jellyfin clients.
@joshuaboniface on Mar 8, 2021
Thank you for this list. We are aware of quite a few, but for reasons of backwards compatibility they’ve never been fixed. We’d definitely like to but doing so in a non-disruptive way is the hard part.
Holy fuck what a reply.
Yeah… ignoring potentially leaking peoples private videos for the sake of “backwards compatibility” is wild. No… When you find a critical flaw like that, you should be breaking compatibility purposefully in order to make people update to tooling/programs that support the new more secure functionality.
Oh wow. That is… Bad. And the issue has gone unaddressed for 4 years now?
Would seem so. The project is open source, and nobody is getting paid. So the lack of update makes sense to some extent.
As cool as it is… and as much as I want to make plex shove it completely. Jellyfin just isn’t ready for prime-time.
I run both… Jellyfin isn’t allowed to talk outside of my network at all, and I can access it over my personal VPN… But Plex is where all my users are because anything else would just be too annoying to maintain.
Holy shit. Thanks. I actually had it exposed as I wanted some of my Plex users to basically beta test my Hardware acceleration config on Jellyfin (another reason why I won’t switch anytime soon) but I just shut that thing down and won’t touch it until I absolutely have to
You are reading too much into the issue linked.
In order to actually abuse any of the unsecured endpoints, you need to have knowledge of the domain, the media/user/stream IDs and media paths. You don’t get those unless you have a user on the Jellyfin instance and brute forcing them is not practical. If you trust the users you add to your Jellyfin instance, there is not much risk in exposing it to the internet.
Those issues definitely need to be addressed at some point, but it doesn’t make Jellyfin exposed on the internet open to anyone.
No… and you’re trusting this WAY too much. This is exactly why it’s dangerous.
You don’t need any knowledge of the domain. Tools like shodan will categorically identify EVERY jellyfin instance that scanners will run into.
the media/user/stream IDs and media paths.
No. Read the whole thread. https://github.com/jellyfin/jellyfin/issues/5415#issuecomment-2525076658
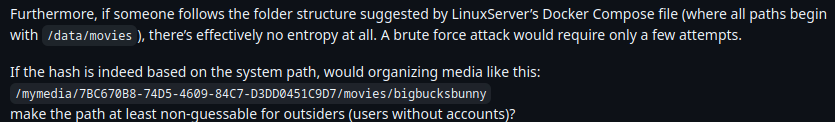
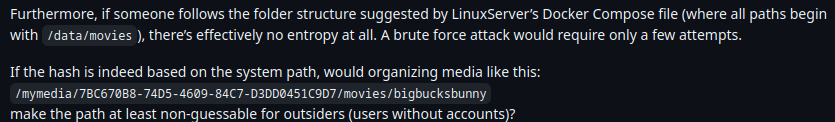
If your path is similar to my path, which due to the nature of the software we ALL have similar paths. You can absolutely bruteforce the CALCULATED AND NOT RANDOM MD5 hash of the folder names that bigbucksbunny lives in. All it takes is for one angsty company to rainbow table variants of their movies name to screw you completely over. This is “security through obscurity”. This isn’t safe AT ALL.
Edit: Just to clarify you would have to ADD your own GUID style information to the folder path in order to make it so a generic precompiled rainbow table for common paths to not work. Eg, /mnt/53ec1945-55dd-4b73-8e03-9e465d5739c3/movies/bigbucksbunny
common paths/names can be setup based on the defaults for programs like the *arrs with minor linux-minded variants and I bet it would hit a good chunk of users who run jellyfin.
and you’re trusting this WAY too much.
I don’t need to trust because I know how it works: https://github.com/jellyfin/jellyfin/blob/767ee2b5c41ddcceba869981b34d3f59d684bc00/Emby.Server.Implementations/Library/LibraryManager.cs#L538
Tools like shodan will categorically identify EVERY jellyfin instance that scanners will run into.
They can’t. Without the domain, the reverse proxy will return the default page.
No. Read the whole thread.
I did.
If your path is similar to my path
It does not need to be similar, it needs to be identical.
- There are 2 popular Docker images, both store the media in different paths by default
- You do not have to follow the default path
- The server does not even have to run in Docker
- The sub path is entirely defined by the user
- You do not know the naming scheme for the content
There are 1000s of variations you have to check for every single file name, with 0 feedback until you get a hit. After you have gone through all that trouble, you can now confirm that the file exists and do great things like retrieve the cover art or the subtitles. None of which is incriminating or useful.
All it takes is for one angsty company to rainbow table variants of their movies name to screw you completely over.
My threat model does not include “angsty company worried about copyright infringement on private Jellyfin servers”.
Why bother scanning the entire internet for public Jellyfin instances when you can just subpoena Plex into telling you who has illegal content stored?
I don’t need to trust because I know how it works: https://github.com/jellyfin/jellyfin/blob/767ee2b5c41ddcceba869981b34d3f59d684bc00/Emby.Server.Implementations/Library/LibraryManager.cs#L538
Yes… exactly how I said it works. Notice the return.
return key.GetMD5();
It’s a hash, not a proper randomized GUID. But thanks for backing me up I guess? I wasn’t interested in posting the actual code for it because I assumed it wouldn’t be worth a damn to most people who would read this. But here we are.
They can’t. Without the domain, the reverse proxy will return the default page.
You are wrong, but at this point I’d have to educate you on a lot of stuff that I don’t have the time or care to educate you on. The tools are out there and it’s beside the point at all, proper auth fixes all the concerns. If it’s publicly accessible you have to assume that someone will target you. It’s pitifully simple for someone to setup a tool to scan ranges and find stuff(especially with SSL registrations being public in general, if I asked any database for all domains issued that start with “jf” or “jellyfin” or other common terms, I’d likely find thousands instantly). Shodan can and does also do domain stuff.
There are 2 popular Docker images, both store the media in different paths by default
So they’d only have to have 2 hashes for a file to hit the VAST MAJORITY OF PEOPLE WHO USE THE DOCKER. What an overwhelming hurdle to jump…
You do not have to follow the default path
Correct, but how many people actually deviate? Forget that most people will map INTO the container and thus conform to the mapping that the containers want to use. This standardizes what would have been a more unique path INTO a known path. This actually makes the problem so much worse.
The server does not even have to run in Docker
And? Many people are simply going to mount as
/mnt/moviesor other common paths. Pre-compiling md5 hashes with hundreds of thousands of likely paths that can be tested within an hour is literally nothing.You do not know the naming scheme for the content
Sure, but most people follow defaults in their *arr suite… Once again… the up-front “cost” of precompiling a rainbow table is literally nothing.
It does not need to be similar, it needs to be identical.
Correct but the point that I made is that they would simply pre-build a rainbow table. The point would be that they would take similar paths and pre-md5 hash them. Those paths would be similar. Not the literal specific MD5 hash.
There are 1000s of variations you have to check for every single file name
Which is pitifully easy if you precompile a rainbow table of hashes for the files for in the name formats and file structures that are relatively common on plex/jellyfin setups… especially to mirror common naming formats and structures that are used in the *arr setups. you can likely check 1000 urls in the matter of a couple of seconds… Why wouldn’t they do this? (the only valid answer is that they haven’t started doing it… but could at any time).
My threat model does not include “angsty company worried about copyright infringement on private Jellyfin servers”.
Yes… let’s ignore the companies that have BOATLOADS of money and have done shit like actively attack torrents and trackers to find thousands of offenders and tied them up legally for decades. Yes, let’s ignore that risk all together! What a sane response! This only makes sense if you live somewhere that doesn’t have any reach from those companies… Even then, if you’re recommending Jellyfin to other people without knowing that they’re in the same situation as you. You’re not helping.
Why bother scanning the entire internet for public Jellyfin instances when you can just subpoena Plex into telling you who has illegal content stored?
I thought you knew your threat model? Plex doesn’t hold a list of content on your servers. The most Plex can return is whatever metadata you request… Except that risk now is null because Plex returns that metadata for any show on their streaming platform or for searches on items that are on other platforms since that function to “show what’s hot on my streaming platforms” (stupid fucking feature… aside) exists. So that meta-data means nothing as it’s used for a bunch of reasons that would be completely legitimate. The risk becomes that they could add code that does record a list of content in the future… Which is SUBSTANTIALLY LESS OF A RISK THAN COMPLETE READ ACCESS TO FILES WITHOUT AUTH but only if you guess the magic incantations that are likely the same as thousand of others magic incantations! Like I said though several times. I’d LOVE to drop plex, BECAUSE that risk exists from them. But Jellyfin is simply worse.
You seem wildly uneducated on matters of security. I guess I know now why so many people just install Jellyfin and ignore the actual risks. The funny part is that rather than advocating for fixing it, so that it’s not a problem at all… you’re waiving it all away like it could never be a problem for anyone anywhere at anytime. That’s fucking wildly asinine when proof of concept of the attack was published on a thread 4 years ago, and is still active today. It’s a very REAL risk. Don’t expose your instance publicly. Proxied or not. You’re asking for problems.
So I have a NAS running Ubuntu I only keep my movies, my Jellyfin, and torrent software on in an isolated VLAN I stream from. I would think this would make any security issue with Jellyfin a dead end. I stream all content from Jellyfin domain I made and never use it locally. I stream off it at home from my VPN. This seems a safe way to stream where it can be used away from home unless I am missing something? Pointing out any holes in my logic is appreciated.
If it’s a private VPN, you should be fine. If it’s publicly accessible the jellyfin access through a vpn itself doesn’t matter. They can just subpoena a request to your domain registrar to get your information since the IP won’t yield anything useful for them.
The VPN is a paid no-log VPN out of Panama. The traffic goes through the VPN applied to the VLAN and my device I stream to uses a different connection to the same VPN service. The domain is a DDNS.
The domain is a DDNS.
Eh, if that’s operating in the US (or other country that cares), they may still give up the mapping to a legal request.
Install tailscale on your server
Install tailscale on their device
Thats it
Cool… point me to the LG TV tailscale app… or the roku tailscale app…
SDNs in general are no different. App support is limited, specifically on devices that people are most likely to want to watch media content on.
And to say that tailscale is “that’s it” is a bit disingenuous. On my setup (LXC containers) I couldn’t add tailscale even if I wanted without faffing with interface stuff.
I hate this update
- no manual PiP which existed in the previous version. The auto PiP works sometimes
- multiple freezes, seemingly random
- phone gets way hotter and drains battery faster
- looks like yet another generic streaming app “experience”
If only Jellyfin onboarding was as easy for friends and family…
If only Jellyfin onboarding was as easy for friends and family…
What makes it harder is that you can’t just expose it to the internet… https://github.com/jellyfin/jellyfin/issues/5415
In order to use Jellyfin you now have to get all your users onto a vpn or some other tunneling service. It’s crazy.
I have both installed… I want to deprecate Plex SO FUKCING BAD. But Jellyfin just isn’t good enough.
If the fact that a 128-bit value when sent to your server can retrieve a single piece of media or user info then I have real bad news about what you can do with a typically much shorter password.
Is it ideal that you can retrieve streams or user info from Jellyfin if you know the ID of the entity you’re looking for? No, obviously not. But you need to authenticate to get those IDs in the first place, and there are fewer bits of entropy in most people’s passwords than there are in UUIDs.
Being able to get streams unauthenticated by guessing the correct UUID is arguably still better security than using passwords without 2FA.
are in UUIDs.
It’s not a UUID. Those tokens are MD5 hashes of values that can be pregenerated (rainbow tabled) or guessed. It’s not random. https://github.com/jellyfin/jellyfin/issues/5415#issuecomment-2525076658
Edit: and UUID in the URL still means capture-able by google search and other issues/crawlers. But somehow security through obscurity is “secure” to you. Y’all are crazy.
My mistake then, it’s more vulnerable then I initially thought. I also don’t think it’s secure even if that weren’t true, just that it’s not worse than single factor passwords (which you also shouldn’t use of security is a concern).
Thanks for admitting it. A few people simultaneously responded attacking my warning. So rereading my response to you, I recognize I was a bit more snarky than was warranted, and I apologize for that.
But yeah, 2fa (Even simple TOTP) baked in would go a long way too on the user front too.
It’s clear that Sony could just generate a rainbow table of hashes in MD5 with common naming conventions and folder conventions, make a list of 100k paths to check or what have you for their top 1000 movies… and then shodan(or similar tool) to finding JF instances, and then check the full table in a few hours… rinse repeat on the next server. While that alone shouldn’t be enough to prove anything, the onus at that point becomes your problem as you now have to prove that you have a valid license for all the content that they matched, they’ve already got the evidence that you have the actual content on your server, and you having your instance public and linkable could be (I’m not a lawyer) sufficient to claim you’re distributing. Like I can script this attack myself in a few hours (Would need a few days to generate a full rainbow table)… Put this in front of a legal team of one of the big companies? They’ll champ at the bit to make it happen, just like they did for torrents… especially when there’s no defense of printers being on the torrent network since it’s directly on your server that exists on your IP/domain.
Wow, this can only be a disaster. People on the Plex experience preview forum are pissed. The android build hasn’t been updated in a month, I didn’t think it would be rolled out for another 3-6 months.
So many features are missing, the only way to remove Plex rentals/free is by going into your account settings, performance is shit even just scrolling your media.
I haven’t looked at the beta client in a while and was wondering how they could’ve gotten it ready this fast. Guess I’ll pin my app version real quick.
Damn it, I don’t want to switch to Jellyfin
It’s simple, Plex is owned by capitalists, their goal is not to provide a service or a product, their goal is to make money. Jellyfin is currently the best as far as I know for doing the only thing anyone ever wanted Plex to do.
This update is so good that I switched my server to jellyfin. I didn’t like it last time I used it, but it seems that they made a lot of improvements and now the app is kinda fire
Jellyfin also just rolled out an update, where’s that post?
You know you can just… post about it yourself, right?
No I don’t know how
If only you had some way to look it up, some sort of big network that could be used to share information. I’d call it the infowebs, but I suppose it will remain a fantasy…
I thought that was just for porn?
🤣
I’d imagine you need a bit of know-how to make good posts.
Wonder how many things they shit up
I was surprised to find that an old Plex feature, controlling any one player from any other instance, such as playing on a laptop and controlling with a cell phone, no longer worked. My wife and I used that a lot when traveling, as plugging a laptop into a hotel TV with an HDMI cable is generally far more bullet proof than any streaming stick
Course sometimes we’d stay in an Airbnb, and they’d have a Roku or Apple TV, where we’d just sign into a Plex app and use it there. But that’s beyond the point
I already switched to jellyfin after the last monthly cost for stream online.
How do people feel about Emby as an alternative?
The full feature is paid. Not saying that thats not fair, but jellyfin is completely free
I use it and enjoy it more than plex tbh. The ads are a little annoying but I’d rather an ad for an app I’m currently using and enjoying than anything else. As soon as they go the plex route though, which will happen, I’m switching to jellyfin
Maybe they’ll finally fix their bugs!











